This last week I’ve been working on getting Drupal running through NGINX so I can test out a page builder feature. I was getting a weird error with the dev-server built into PHP.
I didn’t want to have NGINX running on Windows, so I spun up a VM. Setting up an environment can be time consuming and sharing content between host and client is a bit of a pain.
The last two weeks has had a theme: environment/tools setup. So my mind has been on “how do we improve this process?”
Documenting the process helped a little, but it is still a time consuming process. It also seems like there’s always some new gotchas that eat up time. If only there was a way to automate this…
Here is where Docker enters the picture and where it’s suppose to shine. We can create a group of containers that run a web server, database, and other needed services. This setup can be shared across workstations so we maintain a consistent work environment. We can also use Docker in production too with Amazon’s ECS (Elastic Container Service).
It sounds like a smart move and everyone is on board.
Great, now let’s tear down this idea and look at use cases and scenarios, starting with security.
But in order to feel out security we need to know what Docker is. That can be a little confusing. To be honest, I’m still a bit fuzzy.
My understanding is a Docker container is a very thin layer that can have libs and executables. When you run the container the processes run in their own isolated namespaces.
This diagram is the most helpful of everything I’ve come across.
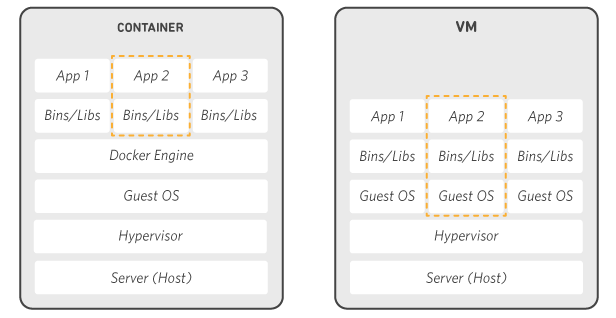
One thing that’s confusing is images (that containers are spun up from) often have a base OS image defined. That image is not the full OS, but rather the bins/libs shown in the container example above.
To understand Docker, images, and containers, the following articles/video may also help:
- What’s under the hood of Docker? (video talk by Janos Pasztor)
- How is Docker different from a virtual machine? (Stackoverflow)
- Synk recommended security practices
What I’ve gathered is containers still need to be maintained for security purposes. Libs and executables may have flaws that need to be patched. However, the surface area for exploits is greatly reduced because containers have only what’s necessary for the app running inside them and the processes are isolated.
I still have some research I need to do on the Docker containers for security. For example, finding something that notifies us when a vulnerability is found would be helpful.